Welcome to the fascinating world of ethical hacking, where curiosity meets cybersecurity. In this beginner-friendly guide, we embark on a journey to uncover the art of footprinting – a foundational skill for every aspiring ethical hacker.

Before starting this course, please have a look at complete road map for ethical hacking journey and read out frequently asked questions about this journey.
Footprinting, the process of systematically collecting information about a target, lays the groundwork for ethical hacking endeavors. From dissecting website details and harnessing the power of emails to mapping networks and utilizing search engines, each step contributes to building a comprehensive understanding of a digital landscape.
In this guide, we not only explore the techniques of information gathering but also delve into essential practices for protecting your own digital assets. Learn how to disable tools like HTTrack, hide your personal details from the internet, and conduct practical exercises on IP addresses and local hosts.
We’ll navigate the intricacies of IP addressing, understand the significance of proxies, and master the use of tools like Tor Browser for anonymous browsing. Whether you’re setting up a secure virtual lab or exploring free proxy servers, each section is designed to empower you with practical skills that form the bedrock of ethical hacking.
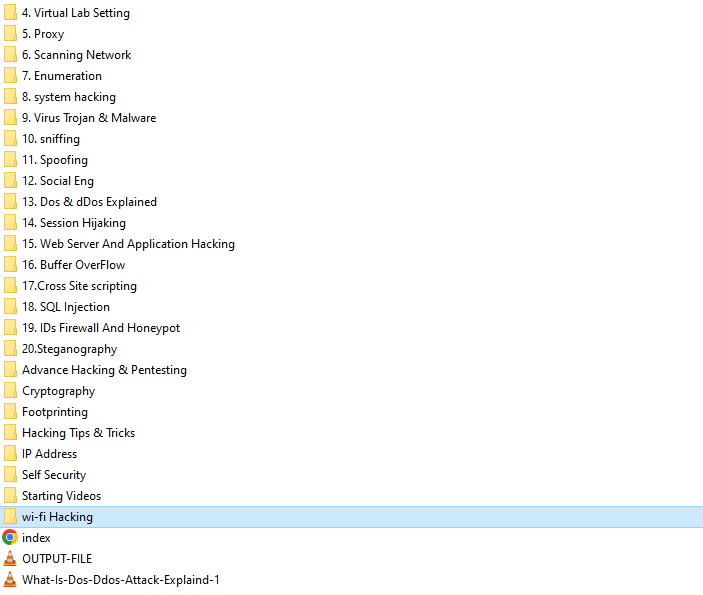
Table Of Contents
Introduction to Footprinting: Tracing Digital Footprints
Welcome to the world of ethical hacking! Footprinting, our first step, involves collecting crucial information about a target. Let’s unravel the basics together.
Get Information from Website Name: Decrypting Domain Secrets
Discover the power of a website’s name! Learn to extract details like domain registration, IP addresses, and hosting providers – vital elements for ethical hackers.
How To Collect Information Using E-mail: Mining Data through Electronic Threads
Explore the realm of e-mails. Uncover methods to extract valuable data, such as associated domains, email server details, and potential vulnerabilities.
Information Collection Using Network: Mapping the Digital Terrain
Dive into network information gathering. Master techniques to map a target’s network, identify active devices, and understand digital interconnections.
Information Gathering Using Search Engine: Navigating the Digital Maze
Search engines are powerful allies. Discover how to efficiently gather information from search engine results, revealing hidden details about a target.
Deep Dive of Footprinting (Conclusion): Connecting the Dots
Conclude your footprinting journey by mastering the art of connecting data points. Learn how to analyze patterns and draw meaningful conclusions for strategic ethical hacking.
How to Disable HTTrack & Web Mirroring: Safeguarding Your Online Presence
Learn essential techniques to protect your websites from potential threats. Disable tools like HTTrack to prevent unauthorized web mirroring and safeguard your digital assets.
Completely Hide Your Personal Details from the Internet: Guarding Your Privacy
Explore practical methods to shield your personal information online. Discover how to maintain control over your privacy and keep your digital identity secure.
Practical of IP Address and Local Host: Hands-On Learning Experience
Engage in real-world scenarios with practical exercises on IP addresses and local hosts. Gain hands-on experience to solidify your understanding of these foundational concepts.
Introduction to IP Address: Decoding the Digital Identifier
Understand the significance of IP addresses in the digital landscape. Explore the basics of IP addressing and its role in internet communication.
Virtual Lab Setting: Creating a Secure Learning Environment
Setting up a virtual lab is crucial for safe and controlled practice. Learn the steps to create a secure environment for hands-on learning and experimentation.
Introduction to Proxy: Navigating Anonymously
Dive into the concept of proxies and their role in anonymous browsing. Understand how proxies enhance security and privacy during ethical hacking activities.
How To Use Tor Browser: Exploring Anonymous Web Browsing
Delve into the Tor browser, a powerful tool for anonymous web browsing. Learn how to use Tor to navigate the internet securely and privately.
How To Use Multiple Proxies: Layered Protection for Enhanced Anonymity
Discover the added layer of security provided by using multiple proxies. Learn the techniques to implement layered proxy configurations for enhanced anonymity.
How To Use Free Proxy Server: Cost-Effective Security Measures
Explore the world of free proxy servers. Learn how to utilize these cost-effective solutions to enhance your security and privacy during online activities.
What Is Scanning: The First Step in Vulnerability Assessment
Gain insights into the scanning phase of ethical hacking. Understand what scanning entails and how it serves as the initial step in identifying potential vulnerabilities.
WiFi Hacking: Unveiling Wireless Vulnerabilities
Explore the art of WiFi hacking, revealing vulnerabilities in wireless networks. Learn techniques to identify and rectify weaknesses ethically.
Honeypots: Tricking the Tricksters
Discover the world of honeypots – decoy systems designed to attract and detect malicious activity. Understand their role in preemptive cybersecurity.
Social Engineering: Mastering Human Manipulation
Delve into social engineering, an art that exploits human psychology. Explore tactics like phishing and impersonation, and understand its role in ethical hacking.

 Stay tuned for exclusive hands-on labs, personal notes, and premium content – all for free!
Stay tuned for exclusive hands-on labs, personal notes, and premium content – all for free! 


1 thought on “Free Certified Ethical Hacking Course (CEH)”
Comments are closed.